Phishing email messages remain the #1 method for hacking groups to deliver ransomware to targeted companies. Phishing campaigns have become more sophisticated, as many of these emails appear to come from a fellow employee or manager. Companies that post senior staff biographies on their website make it easy for hackers to identify managers that other employees trust. Hackers then create and send an email message that impersonates the manager. When employees receive a message that appears legitimate and is from their management team, they naturally trust the sender and click links or open attachments. Malware is downloaded or a backdoor is opened which allows delivery of ransomware.
Simply receiving a phishing email won’t cause any harm, unless a link is clicked in the message body or an attached file is opened. Microsoft Office file attachments (.xlsx, .docx, .pptx) may contain macros (program scripts) that open an Office app then run the macro. These can execute system commands that open network ports and other backdoors, then connect to malicious websites and begin downloading ransomware and encrypting files.
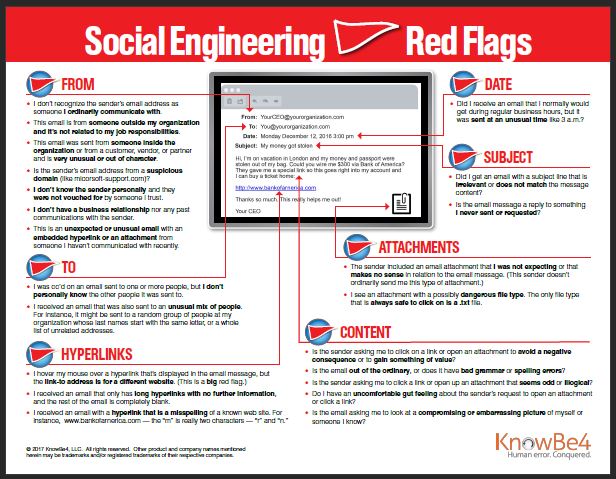
LeeShanok’s partner KnowBe4 created the following chart with many “Red Flags” to watch for when scanning your email inbox. Feel free to download the full size PDF file and share it with your employees.
The US Cybersecurity & Infrastructure Security Agency (CISA) has published a guide on preventing and responding to ransomware: https://www.cisa.gov/sites/default/files/publications/CISA_MS-ISAC_Ransomware%20Guide_S508C_.pdf
LeeShanok’s team hosts monthly web workshops on identifying phishing emails, combating ransomware, and effective backup strategies. Register for the next event on our website: https://www.leeshanok.com/news/events/
As always, feel free to contact us to discuss your situation and industry best practices.
Your technology Partner,
The LeeShanok Team
Phoenix: 602-277-5757 | Tucson 520-888-9122 | itsupport@leeshanok.com
