Insider Tips to Make Your Business Run Faster, Easier, And More Profitably
Topics include: How...
LeeShanok Tech Times – March 2026
Insider Tips to Make Your Business Run Faster, Easier, And More Profitably
Topics include: The...
New Security Service: Microsoft 365 SOC
Business Email Compromise (BEC) incidents have skyrocketed over the past several months. Hackers...
LeeShanok Tech Times – February 2026
Insider Tips to Make Your Business Run Faster, Easier, And More Profitably
Topics include: Your...
LeeShanok Security Upgrade 2026
As part of our ongoing commitment to cybersecurity, we are pleased to announce a significant upgrade...
IT Budget Trends in 2026
The demand for Artificial Intelligence is sending shockwaves through hardware supply chains, in some...
LeeShanok Tech Times – January 2026
Insider Tips to Make Your Business Run Faster, Easier, And More Profitably
Topics include: Hidden...
CAUTION! Hijack of Microsoft 365 Business Accounts
Cybersecurity researchers have discovered a significant spike in advanced phishing...
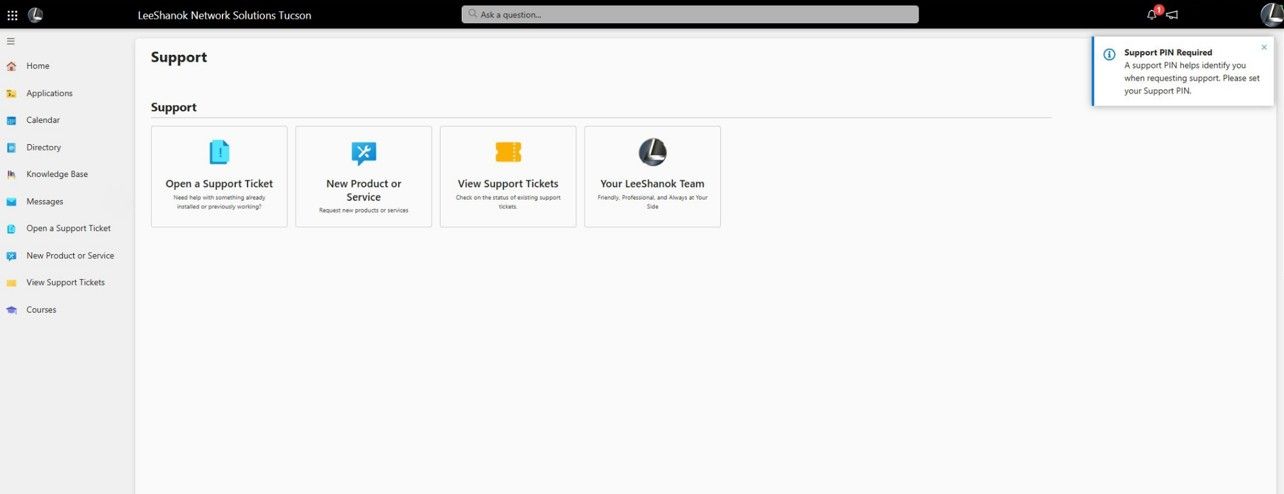
Coming Soon – Get Ready for an Improved LeeShanok Client Experience: New Client Portal!
At LeeShanok, we are excited to announce a significant enhancement to how we partner with your business...
LeeShanok Tech Times – December 2025
Insider Tips to Make Your Business Run Faster, Easier, And More Profitably
Topics include: Holiday...