Gallery – LeeShanok Open House 2024
Thank you to everyone for coming out to tour our new Tucson office! Our guests took a self-guided...
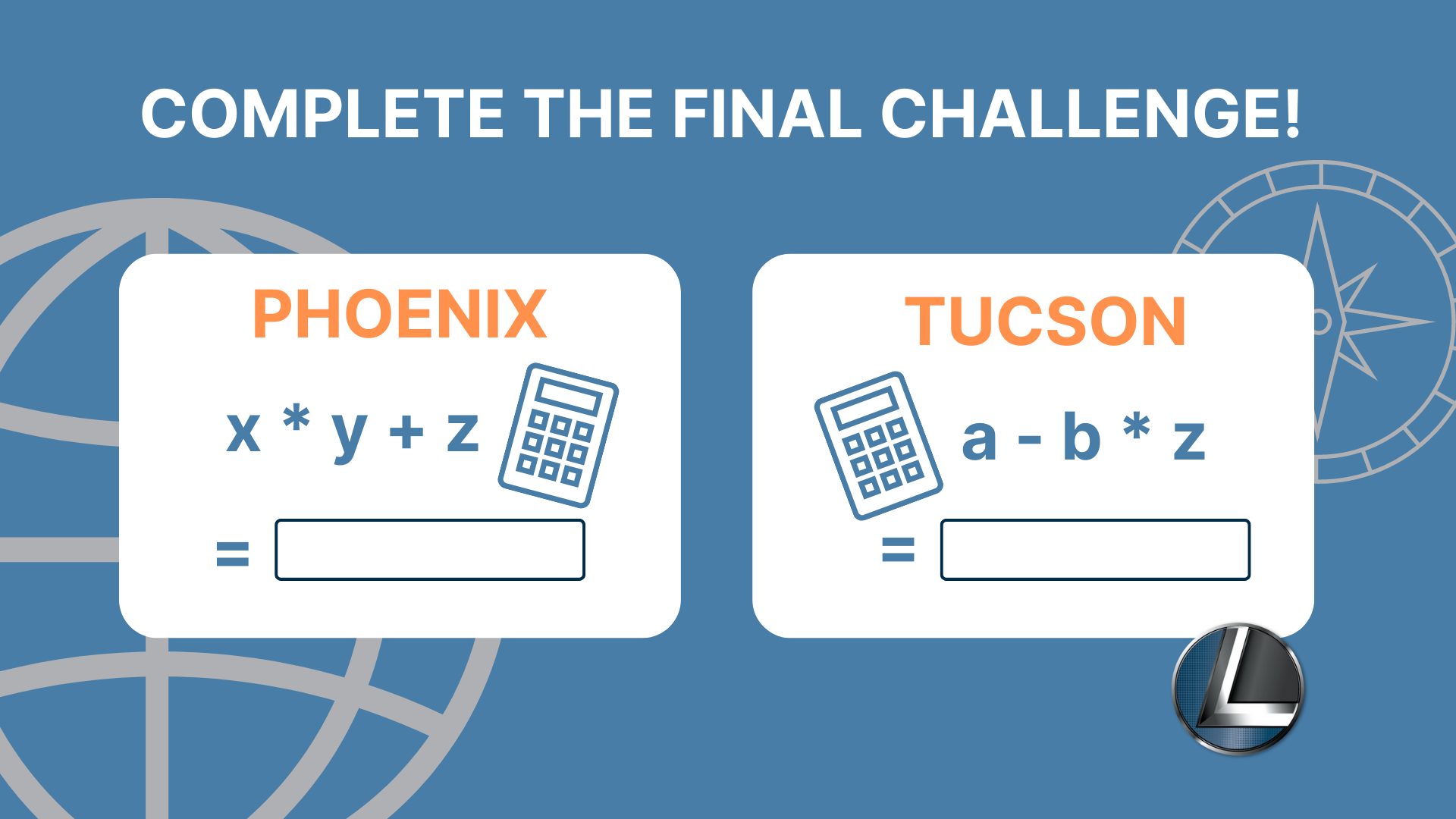
Finish the Hunt!
Finish the Hunt!
You’re Almost There!
Just one more challenge and you’ll have...
Referral Program
LeeShanok Referral Program
LeeShanok Referral Program Details
Client referrals have always...
Privacy Policy
Privacy Policy
Last updated: June 25, 2024
This Privacy Policy describes Our policies and procedures...